Cloud & Infrastructure
Get future ready. Shape and manage the infrastructure that grounds your digital leadership. We’ll help you get the most out of Microsoft’s platform through sound strategy, smooth migrations, optimized performance, and cost-efficiency. Scale with confidence that you can pursue every idea that drives your competitive advantage.
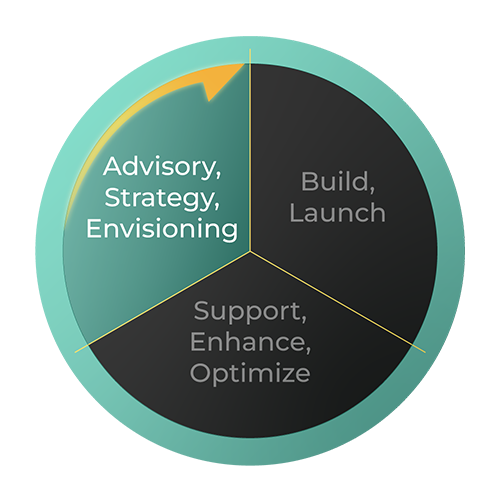
Advisory, Strategy, Envisioning
Cloud & Infrastructure Strategy
- Cloud Infrastructure Landing Zone Assessment
- Cloud Migration Assessment
- Cloud Cost Optimization Assessment
- SQL Server Health Check
WE ALSO PROVIDE TECHNOLOGY BRIEFINGS & READINESS TO ACCELERATE YOUR DIGITAL LEADERSHIP.
- Cloud Infrastructure Landing Zone Briefing
- Cloud Migration Briefing
- Cloud Infrastructure Cost Optimization Briefing
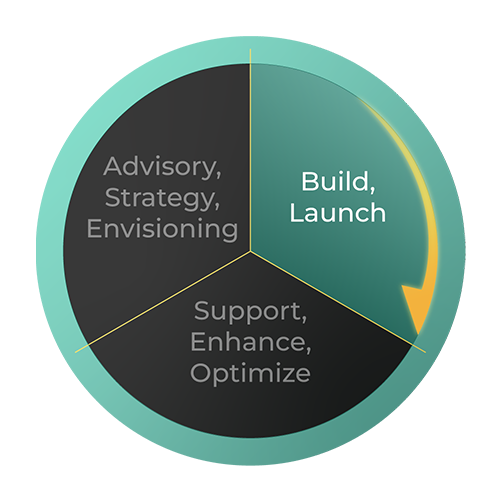
Build, Launch
Cloud Infrastructure Build
- Cloud Infrastructure Landing Zone Build
- Cloud Infrastructure Landing Zone Repair
- Cloud Infrastructure Migration
- Cloud Infrastructure Cost Optimization
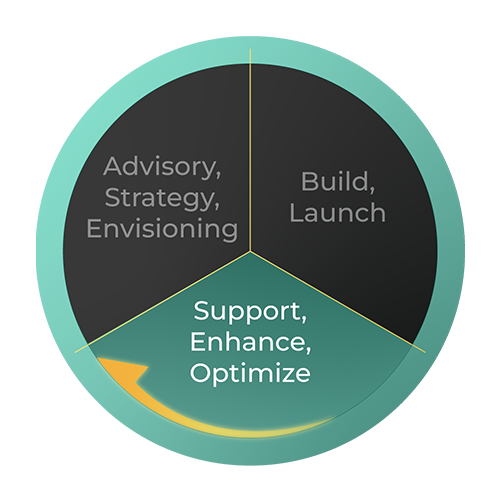
Support, Enhance, Optimize
Cloud Infrastructure Enhance, Support & Optimize
- SQL Server Managed Services
- Cloud Infrastructure Managed Service
- Cloud Infrastructure Cost Optimization Managed Service
Explore our Case Studies
Business Solutions
Inspired Business Solutions
Turn data into a strategic asset. Take the guesswork out of growth and change management. Discover how we tailor our business solutions to help you achieve your strategic initiatives.
Learn More
Contact Us
Let Lantern Advance Your Digital Leadership
We’re here to provide an edge where it’s needed in your technology cycle – from advisory, strategy, and envisioning, through product build and launch, to ongoing support and optimization.
Contact Us
